Establishing your security posture at a given “point-in-time” is a good starting point for organisations to discover their strengths and vulnerabilities. Identifying and rating vulnerabilities means risks can be prioritised and remedied based on potential impact they pose to security and business continuity.
We offer a number of flexible and affordable options to ensure security is for everyone...
Web Application Security Testing & External Penetration Testing

- Information disclosures and memory leaks
- Authentication bypass, logic and race conditions
- PCI-DSS Compliance and Government assurance
- Denial of Service attacks and programming faults
- Validating Role-Based Access Controls (RBAC) for authenticated users.
- Content Management System (CMS) security - Organisation use CMS systems because of the ease of use in maintaining the currency of information across websites, blogs and intranets.
- SQL and LDAP Injection - coding vulnerabilities may allow injection of SQL or LDAP query syntax directly into the backend of your portal, allowing for unexpected manipulation of authentication systems or database information.
- Cross Site Scripting (XSS) - testing for the ability to inject HTML and JavaScript commands, which may be used in phishing attacks against your website users to steal credentials or distribute malware, thereby abusing the trust your website has with its visitors.
- Insecure Upload Forms - websites which accept uploaded content must carefully inspect content from both unauthenticated and authenticated users, as unexpected files may be uploaded such as PHP or ASPX backdoor shells, maliciously infected PDFs and other formats.
Internal Penetration Testing

To protect against Insider Threat, Intellectual Property theft, accidental introduction of worms and other malware;
- Routers and Switching.
- Active Directory and Security Policies.
- Intranet Website and SQL Databases.
- Patch Management and Antimalware.
- Appliances, Servers, Virtual Machines and Workstations.
WiFi Wireless Site Auditing
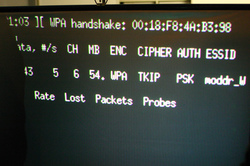
Wireless networking has brought improvements to productivity and the freedom to work from almost any location. The benefits come with risks. Ensuring wireless security protocols are sufficiently secure and both Access Points and clients (i.e. Laptops) are correctly configured and patched will prevent “war-driving” and “man-in-the-middle” attacks.
- Ensuring access points are correctly configured using industry standard protection.
- Dictionary and Brute Force attacks against pre-shared keys.
- Impersonation of a rogue laptop in an attempt to intercept Client-AP communication.
- Exploitation of out-dated Drivers for Windows, OS X and Linux.
- Up-to-date Firmware for Access Points.
Firewall Configuration and Ruleset Auditing
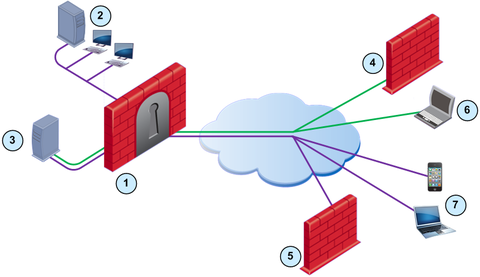
We have experience auditing firewalls for misconfiguration, incorrect order of rules and consolidation, Intrusion Prevention / Detection actions, IPSec and VPNs, device patching, change management and firewall administration policy.
Vendors;
Vendors;
- CheckPoint NGX (Splat & Nokia IPSO / Voyager).
- Cisco PIX and ASA.
- FortiNet.
- IPtables based firewalls.
- Juniper NetScreen (ScreenOS, SRX).
- Symantec Velociraptor.
- SonicWall.
- WatchGuard.
- Whether firewall management methods are adequately secure.
- Ensuring anti-spoofing techniques are implemented on interfaces.
- Determining whether rule-order can be improved to increase performance and throughput.
- Analysis of Out-Of-Band management topology.
- Verification of IPSec VPN configuration and in-transit privacy.
- Firmware upgrade and patch management of firewall platform and Operating System.
- Creation of secure DMZ security zones to segregate networks such as Tier-3 networks.
- Mitigation analysis of network design to minimise impact in the event of successful compromise.
System Hardening, Review and Configuration

We provide installation, configuration and troubleshooting services for any number of operating systems and products.
Linux and OpenSource
We offer services to audit the use of your SOE environment according to best practices, and/or verified against your existing security policy. We have expertise across a wide range of platforms (Windows, Linux, Macintosh, UNIX) and provide many services such as:
Checking the health of your IT Security ensures your exposure to risk and vulnerabilities is reduced. Here are some examples of services offered to clients:
Linux and OpenSource
- Debian e.g. Potato, Woody, Sarge, Etch, Lenny
- RedHat e.g. 6 - 9, Fedora, RHEL
- SuSE and SuSE Linux Enterprise Server (SLES)
- Apple Xserve
- Novell Netware
- Solaris
We offer services to audit the use of your SOE environment according to best practices, and/or verified against your existing security policy. We have expertise across a wide range of platforms (Windows, Linux, Macintosh, UNIX) and provide many services such as:
- OS and third party application patch and vulnerability assessment
- Analysis of all software installed, binaries and libraries for known vulnerabilities
- Verify correct operation of Firewalls, AntiVirus and Intrusion Detection / Prevention Systems (IDS / IPS / NIPS) if present
- Disabling of unnecessary services and/or ports, and ensuring least privileges are used on services to limit exposure
- Detecting possibility of bypassing network security systems to conduct Drive-By Download style attacks over the Internet
- Identification of backdoors and rootkits (if present), exploitation impact mitigation and best practices
- Detection of weaknesses in communications security (ie, no encryption, poor encryption/weak ciphers, flawed protocols)
- Account and password policy auditing (user, service, system etc)
- Incorrect file permissions
- A wide range of other areas depending on the specific environment(s)
Checking the health of your IT Security ensures your exposure to risk and vulnerabilities is reduced. Here are some examples of services offered to clients:
- Regular scheduled on-site visits (i.e. monthly)
- Assess internal network hardware, software and devices.
- Ensure adequate patching of Operating Systems and Software Installed.
- Ensure correct operation of Anti-Malware.
- Other preventative measures based on client requirements.
Electronic Forensics & Data Recovery

We have experience in matters relating to:
- Computer hard disk forensic analysis and reporting.
- Establish whether evidence is present.
- Advice regarding handling of evidence and chain of custody.
- Referral to law enforcement or civil litigation and Expert Witness for Court.
- Data loss and document theft.
- Disgruntled employees.
- Management of Intellectual Property, Classified documents and corporate secrets.
- Investigation of server and network breach.
Vendor Application and Appliance Testing

During the majority of our penetration testing engagements, we are testing the vendor software which the client installed. Whilst a client may be securely configured per best practices, the multitude of vendor products may present a unique risk.
We have experience finding known vulnerabilities, such as default vendor credentials, in addition to zero-day (unknown) vulnerabilities - security risks which are present in the software but not publicly disclosed.
We have experience finding known vulnerabilities, such as default vendor credentials, in addition to zero-day (unknown) vulnerabilities - security risks which are present in the software but not publicly disclosed.
- Ensuring secure configuration.
- Testing for known vulnerabilities.
- Zero-day (0day), undiscovered vulnerabilities, Fuzzing, Stack, Heap Integer Overflows.
- Command Injection attacks.
- Format String memory manipulation.
- Denial-of-Service.
- Backdoors and Default Accounts
Malware and unidentified threat removal

OSI Security's staff have experience in removal of large scale malware breakouts in corporate environments and website infections. Organisations we have assisted include;
- Multinational corporations.
- Not for profit organisations and charities.
- Government bodies.
- Small to medium businesses.
|
|
|